Manifesting Universes with Idealized Mathematical Objects
Abstract
Information technology has enabled humans to inhabit customizable shared fictions of our choosing. Unlike physical reality, these fictions depend on belief in an attesting authority, and when it falters, the shared fiction dissolves. As humans increasingly inhabit these fictions, there is a crucial need for them to exist independently of human belief akin to objective physical reality. Mathematical objects fulfill this need as they exist objectively and independently. In their idealized form, achieved through cryptographic techniques, they would autonomously self-operate, maintain their own secrets, and grow to arbitrary complexity and scale. These idealized mathematical objects may transform dissolvable fictions into mathematically robust, sensorially equivalent, and infinitely customizable universes.
I. IntroductionMore ›
Objective physical reality, governed by immutable natural laws, exists independently of human belief - gravity works whether we acknowledge it or not. This provides a robust foundation to exist on, but at the cost of customization. We cannot edit natural laws to spawn a metallic element with an ideal supply curve and fair distribution across Earth.
As a consequence of nature's immutability, humans transcended objective physical reality to inhabit customizable shared fictions of our choosing. As shown in Figures 1 and 2, information technologies have progressively expanded our capacity to construct shared fictions, and in turn, we have invested more into them.
Unlike physical reality, shared fictions depend on belief in an attesting authority. When this authority falters, as shown in Figure 3, the shared fiction dissolves - often with devastating consequences. Shared fictions offer customization at the cost of robustness.
Figure 1. The progressive development of information technology.






Figure 2. The corresponding increase in scale and sophistication of shared fictions.




Figure 3. The dissolution of shared fictions when belief in the attesting authority collapses.

These shared fictions will become increasingly sophisticated and humans will make increasingly substantial investments into them. Yet even their most advanced forms - generative simulations connected to our sensorium with AI and BCI technologies - remain tethered to belief in an attesting authority.
There is a crucial need for these fictions to exist independently of human belief, and evolve to a form that is as unanimously accepted as objective physical reality itself, so that it can be robust enough to support the extremely substantial investments we intend to make in them.
II. Mathematical PlatonismMore ›
Mathematical Platonism asserts that mathematical objects exist objectively, outside of physical spacetime, and independent of human belief; this allows them to achieve unanimous acceptance on par with physical reality. These objects could fulfill our crucial need.
As shown in Figure 4, mathematical objects have long been used to represent physical reality and successfully act within it, often when shared fictions failed.
Figure 4. The transition from fictional to mathematical representation of physical reality.




Mathematical objects have also been used to go beyond merely representing physical reality to actually manifesting new aspects of reality. Hash functions assign a unique ID to each unique piece of information - akin to fingerprints that everyone sees, with no shared fictions necessary. Digital signatures prove information authorship and are unforgeable, unlike physical signatures. Bitcoin, using hash functions and digital signatures, created a scarcity that objectively exists outside of physical spacetime and independently of belief in any attesting authority.
Taking the "unreasonable effectiveness of mathematics", in both representing our reality but also manifesting new aspects of it, to its logical conclusion reveals a profound implication: all mathematically-consistent universes may objectively exist, with our physical spacetime merely being the particular structure we currently observe. We may eventually manifest and observe the rest, and safely invest in the ones possessing immutable laws of our choosing. However, the mathematical objects we can currently represent are too primitive to manifest such complexity and scale.
III. Idealized Mathematical ObjectsMore ›
Mathematical objects exist abstractly outside of physical spacetime, so we represent them symbolically. Written language enabled static symbolic representation, and electrical encoding advanced it into dynamic symbolic representation. However, significant developments were necessary to harness this into dynamic communication and, now, dynamic mathematical objects.
Networked computing, driven by trillions of dollars of capital expenditure on fiberoptic cables and datacenters, completed communication's evolution from static, primitive text letters to the dynamic, idealized multimedia web of today. The exponential growth of our shared fictions can in many ways be attributed to this evolution.
By applying cryptographic techniques as shown in Figure 5 to networked computing, mathematical objects are now similarly evolving from their static, primitive form to their dynamic, idealized endstate. Idealized mathematical objects, if achieved, would autonomously self-operate, maintain their own secrets, serve everyone neutrally, and grow to arbitrary complexity and scale.
Figure 5. The cryptography development tree.
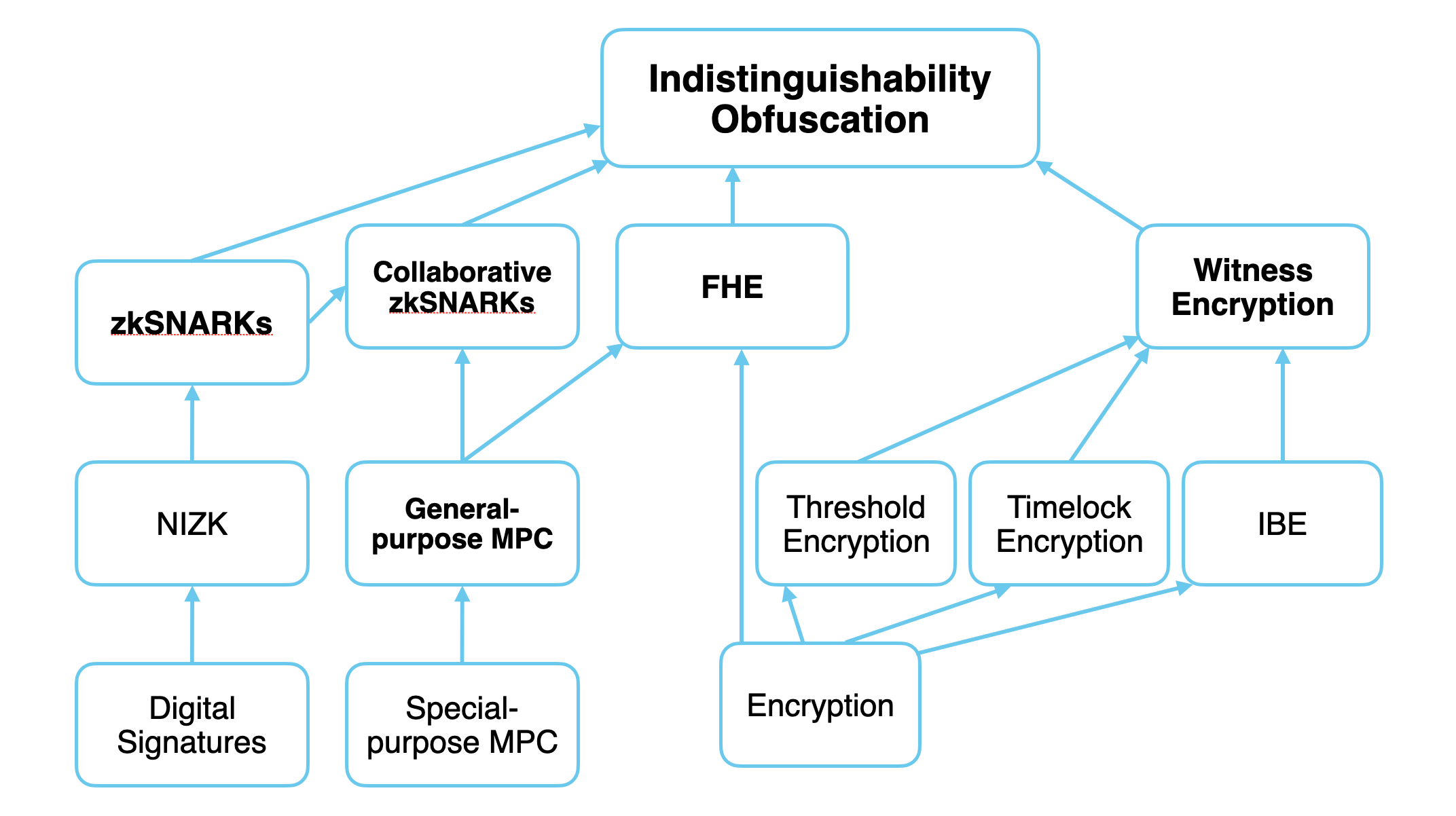
Fully-homomorphic encryption allows computation over a single source of private data without leaking the data or the output of the computation. Multi-party computation allows computation over multiple sources of private data without leaking the data but revealing the output of the computation. zkSNARKs prove correct execution of a computation on inputs kept private by the computer's owner. Witness encryption encrypts a message that can only be decrypted with a proof of a specific computation. Obfuscation allows a party to execute encrypted computation and produce correct outputs without seeing inputs or even the program. From gubsheep's 2024 essay, Programmable Cryptography
IV. ManifestationMore ›
Today, billions inhabit cyberspaces - shared fictions dependent on corporate authorities to exist. This dependence restricts cyberspaces to malleable business logic that only the corporation can upgrade or scale; and, user actions remain temporary event logs that cannot freely connect to their broader lives without the corporation's validation. Our investment in cyberspaces will only grow, so there is a crucial need to remove this dependence.
As shown in Figure 6, idealized mathematical objects operate as immutable laws that exist independently of authority. Users would collectively run, upgrade, and scale the resulting cyberspace themselves. Every user action would become a permanent, objectively verifiable record that permissionlessly connects with their broader lives.
Figure 6. A mathematical cyberspace as a robust foundation for investment.

Servers need administrative control, corporations have financial and legal constraints, and computation requires data visibility. Truly public or truly private computation is not possible. As a result, corporate servers can only implement malleable business logic. This malleability means digital symbols cannot objectively achieve the properties of physical matter - non-fungibility, scarcity, embodiment, and intrinsic value. Furthermore, only corporate servers can validate state and actions within a cyberspace - Twitter can assert your follower count, Bob cannot. As a result, only the corporate authority can implement upgrades or operate servers, and users cannot freely share data or exchange assets beyond the system's boundaries without the corporation's permission.
(B) An idealized mathematical object operates as Digital Physics, man-made laws which are immutable, unbreakable, and contain unleakable secrets. They perform both truly public and truly private computation. This grants physical properties to digital symbols, and may culminate in creating Digital Matter itself - nonfungible, scarce, embodied, and intrinsically valuable within Digital Physics. (C) (D) Digital Physics and Matter create credibly neutral rules and systems of value inside of which user actions become permanent, objectively verifiable records that permissionlessly connect to their broader lives. For example, users within the cyberspace can: configure a door to a building to only open for top posters on a subreddit, or secure a real money loan using a chest filled with Emerald Ore configured as collateral. (A) Beyond participation, user can even contribute resources and propose upgrades to the cyberspace itself.
(B) An idealized mathematical object operates as Digital Physics, man-made laws which are immutable, unbreakable, and contain unleakable secrets. They perform both truly public and truly private computation. This grants physical properties to digital symbols, and may culminate in creating Digital Matter itself - nonfungible, scarce, embodied, and intrinsically valuable within Digital Physics. (C) (D) Digital Physics and Matter create credibly neutral rules and systems of value inside of which user actions become permanent, objectively verifiable records that permissionlessly connect to their broader lives. For example, users within the cyberspace can: configure a door to a building to only open for top posters on a subreddit, or secure a real money loan using a chest filled with Emerald Ore configured as collateral. (A) Beyond participation, user can even contribute resources and propose upgrades to the cyberspace itself.
As societies emerge in the cyberspace and connect to users' broader lives, Digital Matter - required for all user actions - accrues value. This incentivizes users with stakes in the emergent societies to contribute resources and implement upgrades. Through these collective improvements, the mathematical object defining the cyberspace evolves towards its idealized endstate with the complexity and objectivity of an entire universe.
Ultimately, the transition from dissolvable fictions to idealized mathematical objects may culminate in manifesting the other possible universes - mathematically robust, sensorially equivalent, and infinitely customizable - based on their capacity to support and enrich our experience.